Aave V4 Security Audit Clears Code After $1.5M, 345-Day Review
0
0

This article was first published on The Bit Journal.
Aave V4 security audit plays a key role in the preparation for the protocol’s upcoming upgrade, with Aave Labs committing about $1.5 million to a large security review before the launch. The process lasted for nearly 345 days and involved detailed testing and technical verification. Internal developers, well-known security firms, and hundreds of independent researchers all took part in examining the protocol’s code from different perspectives.
This long review process highlights how decentralized finance projects are now placing a stronger focus on safety, stability, and long-term reliability as the industry grows. The review process included several layers of checks such as professional audits, formal verification, automated security testing, and a public contest that allowed outside researchers to examine the system.
More than 900 researchers eventually joined the testing effort and submitted over 950 findings after studying the codebase. Even after such extensive examination, the results showed no validated critical or high-severity vulnerabilities. These findings have strengthened confidence that the protocol is technically prepared as it moves closer to the release of its next version.
How does the Aave V4 security audit reflect the protocol’s security-first development model?
The Aave V4 security audit shows how the protocol changed its earlier development approach. Instead of following the common method used by many early DeFi projects, where products are built first and audited later, the team included security checks throughout the development process. The program was supported by a $1.5 million security budget approved by the Aave DAO.
With this funding, security reviews were carried out alongside development rather than being saved for the final stage before launch. Several established security firms were involved in the review process, including ChainSecurity, Trail of Bits, Blackthorn, and Certora. Rather than conducting a single audit, the project went through multiple layers of evaluation. Internal developers, external auditors, and independent researchers examined different parts of the system, including the protocol’s architecture and its smart contracts.
The security reviews carried out by these firms did not identify high-severity vulnerabilities in the code that was examined. These results helped prepare the protocol for the next stage of testing, which involved broader public participation. The findings also supported the project’s shift toward a development model where security checks remain a continuous part of the building process.
What did the public security contest reveal about the codebase?
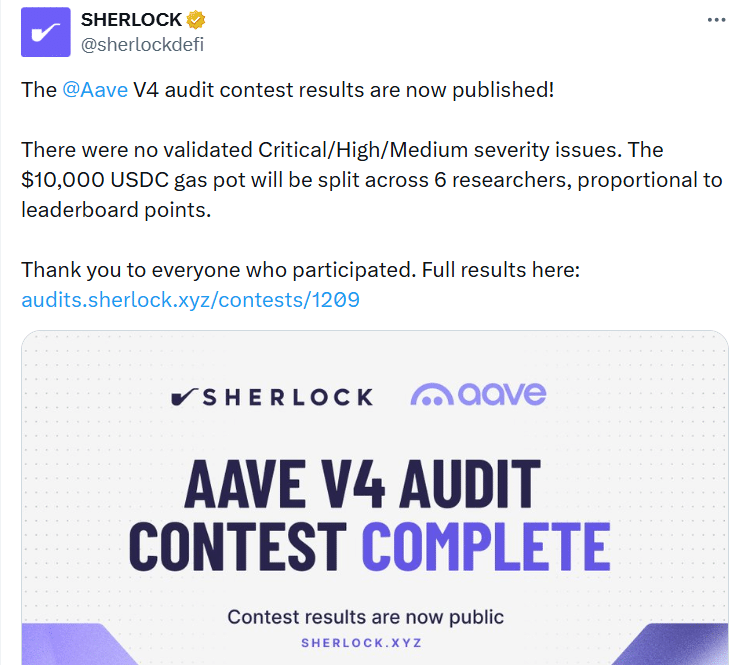
A public contest became one of the most visible phases of the Aave V4 security audit. The six-week program was held on the Sherlock platform between December 2025 and January 2026 and invited independent researchers to study the smart contracts and look for possible vulnerabilities. More than 900 verified participants joined the effort and together submitted over 950 findings while reviewing the protocol’s code.
After the review period ended, Sherlock shared the results and noted that “there were no validated Critical/High/Medium severity issues.” A $10,000 USDC gas pot was later divided among six researchers based on their positions on the leaderboard. This outcome added another layer of public verification to the earlier professional security reviews. The contest also helped demonstrate the strength of the protocol’s architecture after extensive examination by a large community of security researchers.
How did the multi-stage review timeline strengthen the audit process?
The security program behind the Aave V4 security audit progressed through several stages, with each phase reviewing the code from a different angle. The process started with planning for formal verification and an early review of the protocol’s architecture. Certora worked alongside developers to define strict invariants, which are mathematical conditions that the smart contracts must always meet.
The first major audit phase took place between September and November 2025. During this period, firms such as ChainSecurity, Trail of Bits, and Blackthorn carried out manual code reviews and technical testing of the protocol’s mechanisms. After this stage, the public Sherlock contest ran from late 2025 into early 2026, giving hundreds of independent researchers the opportunity to examine the system.
Once the contest ended, developers reviewed the submitted findings and implemented fixes where necessary. The code then went through another round of review in early 2026 to confirm that the updates had not created new security issues. This structured process created several layers of verification instead of relying on a single review before launch.
What long-term security commitments emerged from the audit program?
The experience gained through the Aave V4 security audit has encouraged Aave Labs to outline a long-term plan focused on maintaining strong security standards as the protocol continues to evolve. This plan highlights five ongoing commitments that are expected to guide future upgrades and development work. One of the key elements is keeping formal verification involved from the earliest stages of development so that possible vulnerabilities can be detected before the code moves to later audit stages.
The protocol will also continue using layered security reviews, which combine manual audits, automated testing systems, and participation from independent researchers. In addition, continuous verification tools will monitor code changes during development cycles to ensure that updates do not introduce unexpected risks.
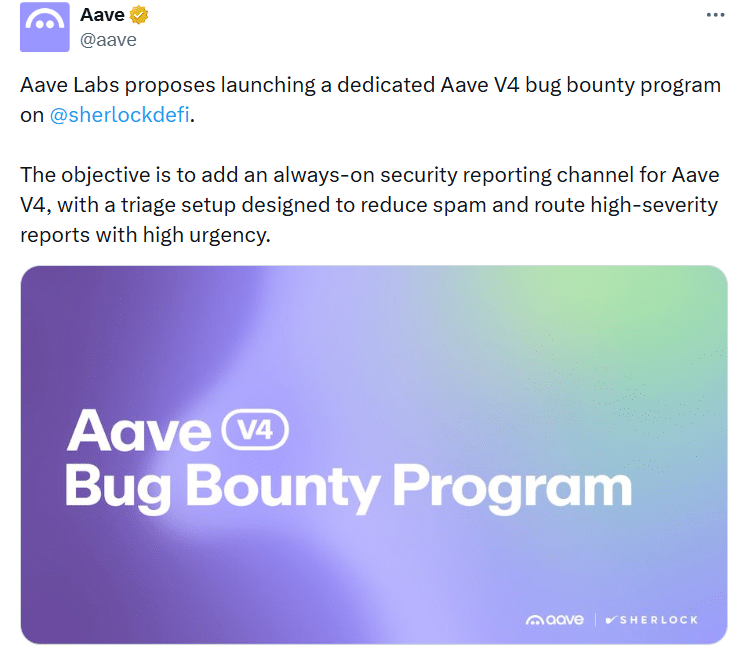
The protocol is also planning to introduce a permanent bug bounty program. In a post shared on X, the Aave team proposed launching a dedicated bug bounty initiative on Sherlock to create “an always-on security reporting channel for Aave V4,” with a triage process designed to quickly route high-severity reports. Developers also plan to further expand AI-assisted tools that scan smart contracts to identify unusual patterns or possible attack paths during development.
Why is the new architecture important for security?
The upcoming version introduces a redesigned hub-and-spoke architecture aimed at lowering the protocol’s overall attack surface. Compared with earlier versions, the V4 codebase is built to be smaller and more modular. This structure allows auditors to examine separate components more easily and identify potential vulnerabilities without affecting the entire system.
A modular design can also help contain problems if an issue appears in a specific component. For protocols that manage large amounts of liquidity, reducing interconnected risks is seen as an important step for stronger security. Researchers who looked at parts of the code during development noted that the architecture appeared unusually clean for a project at the pre-launch stage. This reflected how security checks were integrated throughout development rather than added only after the code was completed.
What governance developments surround the V4 rollout?
The release of details about the Aave V4 security audit comes at a time when discussions within the Aave ecosystem are ongoing about governance and the future direction of development. BGD Labs, a long-time technical contributor that helped build important parts of the protocol’s infrastructure, recently said it plans to step away from Aave-related work after around four years of involvement.
The Aave Chan Initiative (ACI) founder Marc Zeller also said that the Aave Chan Initiative plans to exit the protocol in July as disagreements among contributors have increased. These developments followed debates around a governance proposal called “Aave will win,” which presented revenue adjustments and broader plans connected to the V4 upgrade.
The proposal passed a temperature check vote with 52.6% support, showing that opinions within the DAO are divided. Some observers believe that if these governance differences continue, coordination around future upgrades or quick security responses could become more challenging, even though the current audit process remains technically strong.
What risks remain despite extensive audits?
Security reviews can greatly lower the chances of vulnerabilities, but they cannot completely remove every possible risk. The Aave V4 security audit examined known types of smart contract weaknesses through methods such as formal verification, manual security checks, and public testing. Even with these efforts, decentralized finance systems function in complex environments where interactions with other protocols can sometimes create unexpected issues.
Connections between different DeFi platforms, flash-loan strategies, and changes at the governance level can produce situations that are difficult to fully predict before launch. Because of this, the first few months after deployment will serve as an important real-world test for the protocol’s architecture and its overall security framework.
Conclusion
Aave V4 security audit represents one of the most extensive security initiatives undertaken by a decentralized finance protocol prior to a major upgrade. The $1.5 million program spanned approximately 345 days of testing and involved several professional security firms alongside more than 900 independent researchers who participated in a public contest.
Across professional audit rounds and the Sherlock security competition, no validated critical, high, or medium-severity vulnerabilities were identified. The process also established a long-term security roadmap based on formal verification, layered auditing, continuous testing, bug bounty programs, and AI-assisted scanning tools.
Even so, audits alone cannot eliminate all risk. The long-term effectiveness of the Aave V4 security audit will ultimately be evaluated after deployment, when the protocol operates under real market conditions and sustained liquidity activity across the decentralized finance ecosystem.
Glossary
Formal Verification: Mathematical proof that smart contract code follows strict rules.
Smart Contracts: Blockchain code that runs transactions automatically.
Layered Security Model: Security built using multiple protection layers.
Bug Bounty Program: Rewards given for reporting security flaws.
Flash Loans: Loans borrowed and repaid in a single blockchain transaction.
Frequently Asked Questions About Aave V4 Security Audit
What is the Aave V4 security audit?
The Aave V4 security audit is a large review that checks the protocol’s code to find and fix security problems before launch.
How much did Aave spend on the V4 security audit?
Aave Labs spent about $1.5 million on the security audit for the V4 upgrade.
How many researchers tested the Aave V4 code?
More than 900 researchers studied the code and submitted over 950 findings during the review.
Which companies helped review the Aave V4 code?
Security firms such as ChainSecurity, Trail of Bits, Blackthorn, and Certora helped review the protocol.
Were any critical vulnerabilities found in the audit?
No critical or high-severity vulnerabilities were confirmed during the Aave V4 security audit.
Sources:
Read More: Aave V4 Security Audit Clears Code After $1.5M, 345-Day Review">Aave V4 Security Audit Clears Code After $1.5M, 345-Day Review
0
0
 Verwalten Sie alle Ihre Kryptowährungen, NFTs und DeFi an einem Ort
Verwalten Sie alle Ihre Kryptowährungen, NFTs und DeFi an einem OrtVerbinden Sie sicher das Portfolio, das Sie zu Beginn verwenden möchten.





