Polkadot Hack: Attacker Exploits Ethereum Contract, Mints 1B DOT Tokens
0
0
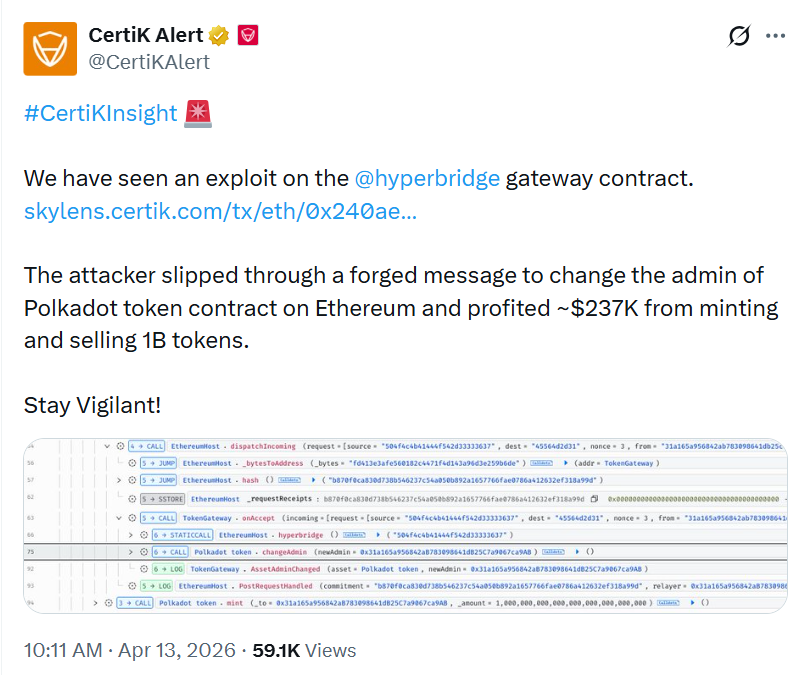
A Hyperbridge exploit exposed a serious flaw in cross-chain messaging on Ethereum. The attack let an exploiter take control of a bridged Polkadot token contract. Security firm CertiK flagged the incident after tracing the attack path on-chain.
The breach centered on Hyperbridge’s gateway contract. The system is part of the ISMP framework, which is used to pass messages between chains such as Polkadot and Ethereum. In this case, the message flow appears to have been manipulated.
Hyperbridge Exploit Used Forged Proofs to Seize Admin Rights
According to the alert, the attacker deployed a master contract and a helper contract in one transaction. The helper then submitted forged stake proofs to the vulnerable HandlerV1 contract. That step appears to have bypassed the expected verification checks.
The forged message moved through the dispatch incoming function. It was then routed to TokenGateway.onAccept. From there, a malicious ChangeAssetAdmin action was executed on the bridged DOT token contract.
This gave the attacker admin and minter rights. Once those privileges were transferred, the contract was fully exposed. The attacker could then mint tokens without a valid cross-chain backing.
Admin Takeover Opened the Door
The core issue appears to be in proof validation. The request receipts check should have matched the message against a valid state commitment from Polkadot. Instead, on-chain traces suggest the stored commitment value was all zeros.
That detail points to a missing or bypassed verification step. The gateway still accepted the message as real. After that, the token contract executed a changeAdmin call and handed control to the attacker’s address.
This was the turning point in the Hyperbridge exploit. Once admin control was lost, the attacker gained the ability to issue tokens at will. That made the rest of the exploit fast and direct.
One Billion Tokens Were Minted
After the admin change, the attacker minted 1 billion DOT tokens in a single transaction. That figure was far above the reported ERC-20 DOT supply on Ethereum, which stood at about 356,000 tokens. The scale of the mint made the incident stand out at once.
The newly created tokens were then sold into Ethereum liquidity pools. Etherscan data showed the attacker used Odos Router and Uniswap V4 to swap the tokens. The trades returned about 108.2 ETH.
The ETH was then sent to the attacker’s externally owned wallet. The funds remained there at the time of publication. Based on current prices, the profit was estimated at about $237,000.
Liquidity Limited the Final Damage
The size of the token mint was massive. The final gain, however, was much smaller than the supply figure suggested. That happened because the bridged DOT pool on Ethereum had weak depth.
The attacker sold into a shallow market. The large token amount overwhelmed available liquidity. That pushed execution prices down and sharply reduced the return per token.
In this case, low liquidity worked against the exploiter. It capped the damage and limited the extracted value. On a deeper pool, the same flaw could have produced much larger losses.
The risk would have been even greater if the tokens had reached native DOT markets on Polkadot. That did not happen here. Still, the event showed how dangerous the flaw could have been under different conditions.
Second Incident Raised More Concern
This was not the first attack tied to the same system that day. An earlier exploit reportedly drained about $12,000 in MANTA and CERE tokens. That attack was said to use a similar vector.
The repeated pattern suggests a broader weakness in the ISMP pipeline. The issue appears tied to poor verification of state proofs. If that reading is correct, other connected token contracts may also face risk.
CertiK said the Hyperbridge gateway contract was the attack vector. The firm also confirmed that the exploiter profited by minting and selling the bridged tokens. That added weight to the concern that the flaw was structural, not isolated.
Market Reaction Followed Quickly
Following the incident, DOT fell about 4.8% to $1.16, based on CoinMarketCap data. The drop reflected a fast market response to the exploit. Traders often react quickly when token control and mint authority are compromised.
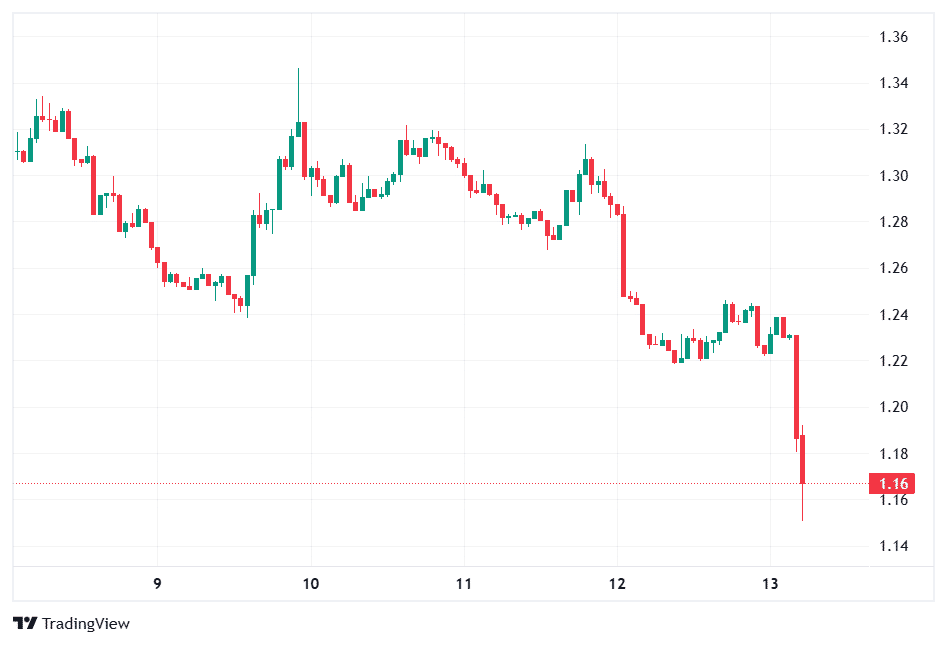
The decline also showed how bridge incidents can affect sentiment beyond the direct contract involved. Even though this exploit targeted the bridged token on Ethereum, it still placed pressure on the wider DOT narrative.
Project Silence Adds to Uncertainty
Hyperbridge was developed by Polytope Labs. The project has described itself as a trust-minimized interoperability layer that relies on cryptographic proofs instead of multisig committees. That model was designed to avoid many common bridge failures.
Yet the exploit showed that cryptographic design alone is not enough. The implementation of proof checks is just as important. A single weak point in validation can undermine the whole security model.
At the time of reporting, no widely circulated public statement had outlined pauses, mitigations, or recovery plans. It also remained unclear whether other bridged assets on the same gateway were exposed. That silence added more uncertainty around the incident.
Conclusion
The Hyperbridge exploit exposed a critical weakness in cross-chain proof validation. The attacker used a forged message to gain admin control, mint 1 billion DOT tokens, and extract about 108.2 ETH.
The incident also raised wider concerns about bridge security. A system built around cryptographic proofs still failed at the verification layer. Until the project addresses the issue clearly, questions about other bridged assets and gateway safety are likely to remain.
Appendix: Glossary of Key Terms
Hyperbridge: A cross-chain interoperability system developed by Polytope Labs.
ISMP: Short for Interoperable State Machine Protocol. It is used to pass messages between blockchains.
Gateway contract: A smart contract that receives and processes cross-chain messages.
HandlerV1: The contract that allegedly accepted forged state proofs in this incident.
State proof: Cryptographic data meant to prove that a message or event is valid on another chain.
Frequently Asked Questions About Hyperbridge Exploit
1: What was the Hyperbridge exploit?
It was a forged cross-chain message attack. The attacker took control of the bridged DOT token contract on Ethereum.
2: How did the Hyperbridge exploit happen?
The attacker used forged state proofs on HandlerV1. That bypassed checks and triggered a malicious admin change.
3: What did the attacker gain?
The attacker got admin and minter rights. That allowed 1 billion DOT tokens to be minted.
4: How much did the attacker make?
The minted tokens were swapped for about 108.2 ETH. The estimated profit was around $237,000.
References
Read More: Polkadot Hack: Attacker Exploits Ethereum Contract, Mints 1B DOT Tokens">Polkadot Hack: Attacker Exploits Ethereum Contract, Mints 1B DOT Tokens
0
0
 Manage all your crypto, NFT and DeFi from one place
Manage all your crypto, NFT and DeFi from one placeSecurely connect the portfolio you’re using to start.